On 31 May 2022, Microsoft disclosed a remote code execution vulnerability in MSDT, the Microsoft Support Diagnostic Tool. This vulnerability, CVE-2022-30190, can be exploited by sending a URL to a vulnerable system. Successful exploitation allows an attacker to install programs, view or change data, or create new accounts in line with the victim’s user permissions. There are a number of proof of concept videos getting around including one that is a bit scary that uses the file previewer in Windows to trigger the vuln. As of 1/6/22 there is no patch from Microsoft.
There are two things you can do to mitigate the vulnerability:
- Remove the ability for ms-msdt: URL’s to be executed
- Disable troubleshooting tools via group policy
Non-mitigated functionality
First, let’s see what happens before the mitigation:
Launch the troubleshooter
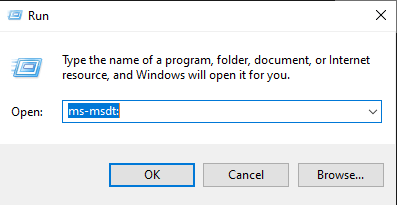
Or run a troubleshooter app from the start menu

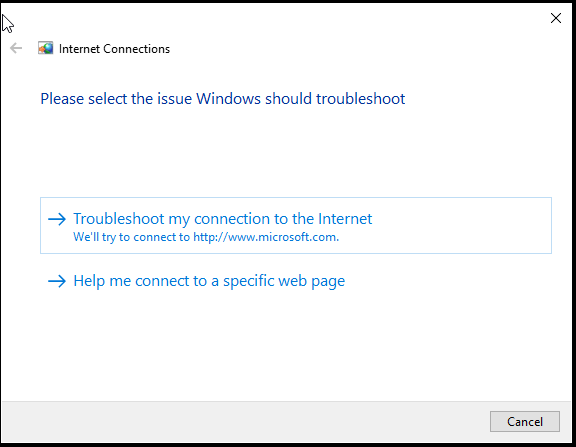
The troublershooter tool runs as expected
Remove ms-msdt functionality
To remove ms-msdt URL functionality, we need the URL to not associate with the %SystemRoot%\system32\msdt.exe binary, this is achieved by deleting the ms-msdt URL handler key from the registry.
Here is the key we are talking about

Since this will be patched at some point, we want a way to be able to revert the change so I captured the default keys and added these to their own collection and targeted them at a computer that doesn’t exist (targeting will be removed once we want the original keys restored):
Original reg keys
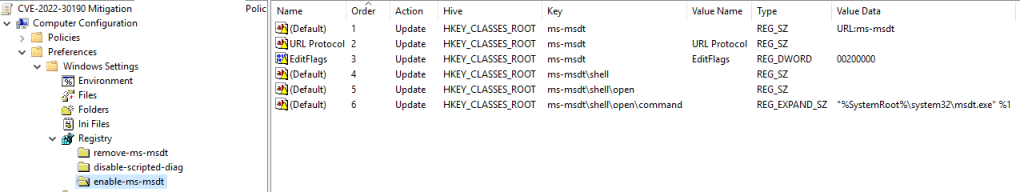
In table form for easy viewing / copying:
| Hive | Key | Value Name | Type | Value Data |
| HKEY_CLASSES_ROOT | ms-msdt | none (default) | REG_SZ | URL:ms-msdt |
| HKEY_CLASSES_ROOT | ms-msdt | URL Protocol | REG_SZ | |
| HKEY_CLASSES_ROOT | ms-msdt | EditFlags | REG_DWORD | 00200000 (hex) |
| HKEY_CLASSES_ROOT | ms-msdt\shell | none (default) | REG_SZ | |
| HKEY_CLASSES_ROOT | ms-msdt\shell\open | none (default) | REG_SZ | |
| HKEY_CLASSES_ROOT | ms-msdt\shell\open\command | none (default) | REG_EXPAND_SZ | “%SystemRoot%\system32\msdt.exe” %1 |
Targeting ‘enable-ms-msdt’ collection to a non existent computer for quick restore of keys once vuln is patched

I then created a collection with the root ms-msdt key that we will be deleting:
ms-msdt key to be deleted

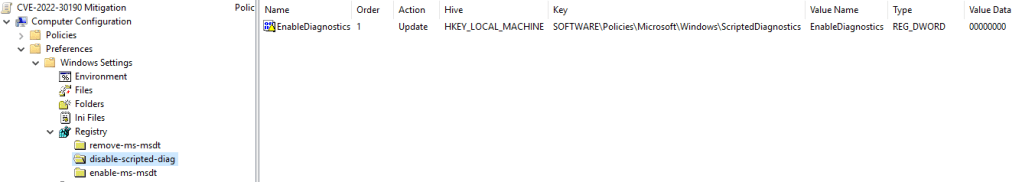
Disable troubleshooting tools
To disable the troubleshooting tools, the following reg key was also deployed: (see link)
EnableDiagnostics reg key to be deployed
Mitigated functionality
Launch the troubleshooter
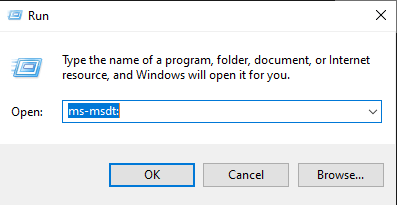
The URL no longer has a handler to execute
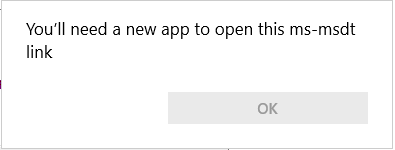
Or run a troubleshooter app from the start menu

Troubleshooter can’t execute as it has been restricted by GPO

Reverting the changes
To revert the changes, all we have to do now is remove the targeting from the enable-ms-msdt collection, delete the collection that is deleting the ms-msdt key and set the EnableDiagnostics reg key to binary 1 which enables users to run troubleshooters again. In my experience the troubleshooters are pretty useless anyway so maybe I’ll leave this disabled.
Thanks for reading.