Recently I had a need to convert a WAV audio file from 22.05Khz, Mono, 8-Bit PCM to Khz, Mono, 16-Bit PCM so that a phone system I was configuring could interpret the audio files used for on-hold messaging.
There are a number of online services that can do this, but I don’t trust them and I wanted to work out how to do this with ffmpeg.
Since I was using my Windows box at the time and I needed to document this for others, I went with the Windows binary, but the same could be achieved on Linux or Mac.
- The windows package for this software can be found here: https://www.gyan.dev/ffmpeg/builds/ffmpeg-git-essentials.7z
- The download will be a .z7 file which will need to be extracted using 7-zip
- Once extracted, browse to the bin folder, eg.
\ffmpeg-2022-06-16-git-5242ede48d-essentials_build\bin - You will see a file called ffmpeg.exe. This is the file that performs the conversion via command line
- Copy the path from file explorer so that you can browse to this location using command prompt or PowerShell
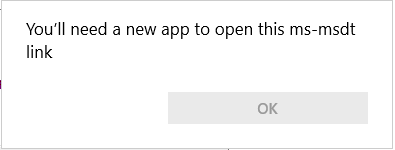
- Open command prompt,
start > run > cmd > enter - In command prompt, change to this directory , eg. cd
C:\ffmpeg-2022-06-16-git-5242ede48d-essentials_build\bin - Now you will be in the bin directory and you can use
ffmpeg - To check what type of file you are working with, run the following command
C:\>ffmpeg.exe -i C:\sample.wav, eg.C:\ffmpeg-2022-06-16-git-5242ede48d-essentials_build\bin>ffmpeg.exe -i C:\users\<user>\downloads\sample.wav - An output will be given showing the encoding of the file.
- If the file is already
8Khz, Mono, 16-Bit PCMthen no changes are necessary and the file can be used. - If the file is something different to this, for example
22050 Hz, mono, u8, 176 kb/s, then it will need converting. - Keep in mind that by default
ffmpegwill output information inHzrather thanKhz. In this example,22050 Hzis22.05 Khz(not what we want!). - The
u8listed in the example is anffmpeg audio type. See this page to identify what audio types there are: https://trac.ffmpeg.org/wiki/audio%20types. - When we check
u8against audio types, it is listed asPCM unsigned 8-bit. Since this is not16-bit, we need to convert the file. - The audio type for
8Khz, Mono, 16-Bit PCMispcm_s16le. - To convert the file, we use the following command
ffmpeg -i sample.wav -acodec pcm_s16le -ac 1 -ar 8000 output.wav, eg:ffmpeg.exe -i C:\users\<user>\downloads\sample.wav -acodec pcm_s16le -ac 1 -ar 8000 C:\users\<user>\downloads\output-16-bit.wav - Let’s break down the command.
-iis for input file,-acodecspecifies the audio codec,-acsets the number of audio channels (mono),-arsets the audio sampling frequency (8Khz) - If we run ffmpeg with no switches against the converted sample file again, we get
8000 Hz, mono, s16, 128 kb/swhich is compatible with phone system I was working on.
Using the same method above, you could convert any number of source audio formats to other formats. Ffmpeg also has many other capabilities and can convert video too, it’s extremely flexible and robust. I recommend checking out the following man page https://manpages.org/ffmpeg.
Lastly, I looked back through my notes and realised I had used ffmpeg a few times in the past. One of these times was to convert a mp4 video file to webm for a HTML5 project, eg.
ffmpeg -i "C:\Users\<user>\Documents\Media1.mp4" -c:v libvpx-vp9 -crf 30 -b:v 0 -b:a 128k -c:a libopus C:\temp\output.webm
Thanks for reading.






You must be logged in to post a comment.